This lab requires a NIOS 9.0 Lab Environment
This lab guide has been developed using the new NIOS 9.0 Lab Environment. Please ensure that you deploy a NIOS 9.0 lab environment to complete these lab tasks. If you use a different lab environment, this is untested, and the lab likely will not work.
Scenario
A corporate compliance policy was created to increase your corporate DNS security posture. The policy dictates what domains will be allowed and which ones will be blocked or modified. Your current task is to create a Pass-thru policy allowing trusted internal domains to be resolved unmodified.
Learning Content
Estimate Completion Time
-
20 to 25 minutes
Credentials
|
Description |
Username |
Password |
URL or IP |
|---|---|---|---|
|
Grid Manager UI |
admin |
infoblox |
Requirements
-
Administrative access to the Grid
Lab Initiation
Access jump-desktop
Once the lab is deployed, you can access the virtual machines required to complete this lab activity. To initiate the lab, click on the jump-desktop tile and login to the Linux UI:
Username: training
Password: infoblox
Initiate lab
To initiate the lab, double-click the Launch Lab icon on the Desktop.
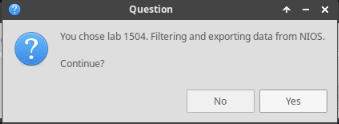
Choose the lab number from the list and click OK.
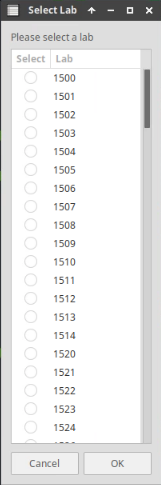
After clicking OK, you will see a pop-up message with a brief description of the lab task. If the description looks correct, click Yes to continue lab initiation.
Lab initiation will take a couple of minutes to finish.
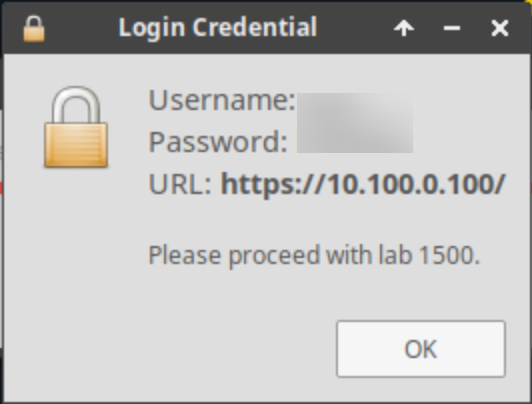
Once complete, you will see another pop-up message with the login credentials and the URL for the Grid Manager’s User Interface. Note that the credentials may differ from those from prior labs.
Tasks
-
Create a local RPZ named allowlist.rpz
-
Create a rule in the allowlist.rpz to ensure DNS requests for techblue.net and all of its sub-domains get passed through unmodified
-
Test Pass-thru Local RPZ Rules
Task 1: Create local RPZ - allowlist.rpz
-
Create a local RPZ named allowlist.rpz to ensure DNS traffic from the techblue.net domain is allowed to pass through using a previously configured server group called RPZ Local NSG.
Task 2: Add Passthru Domain Policy Rules to allowlist.rpz
-
Create a rule in the allowlist.rpz to ensure DNS requests for techblue.net and all of its sub-domains get passed through unmodified.
Task 3: Test Pass-thru Local RPZ Rules
-
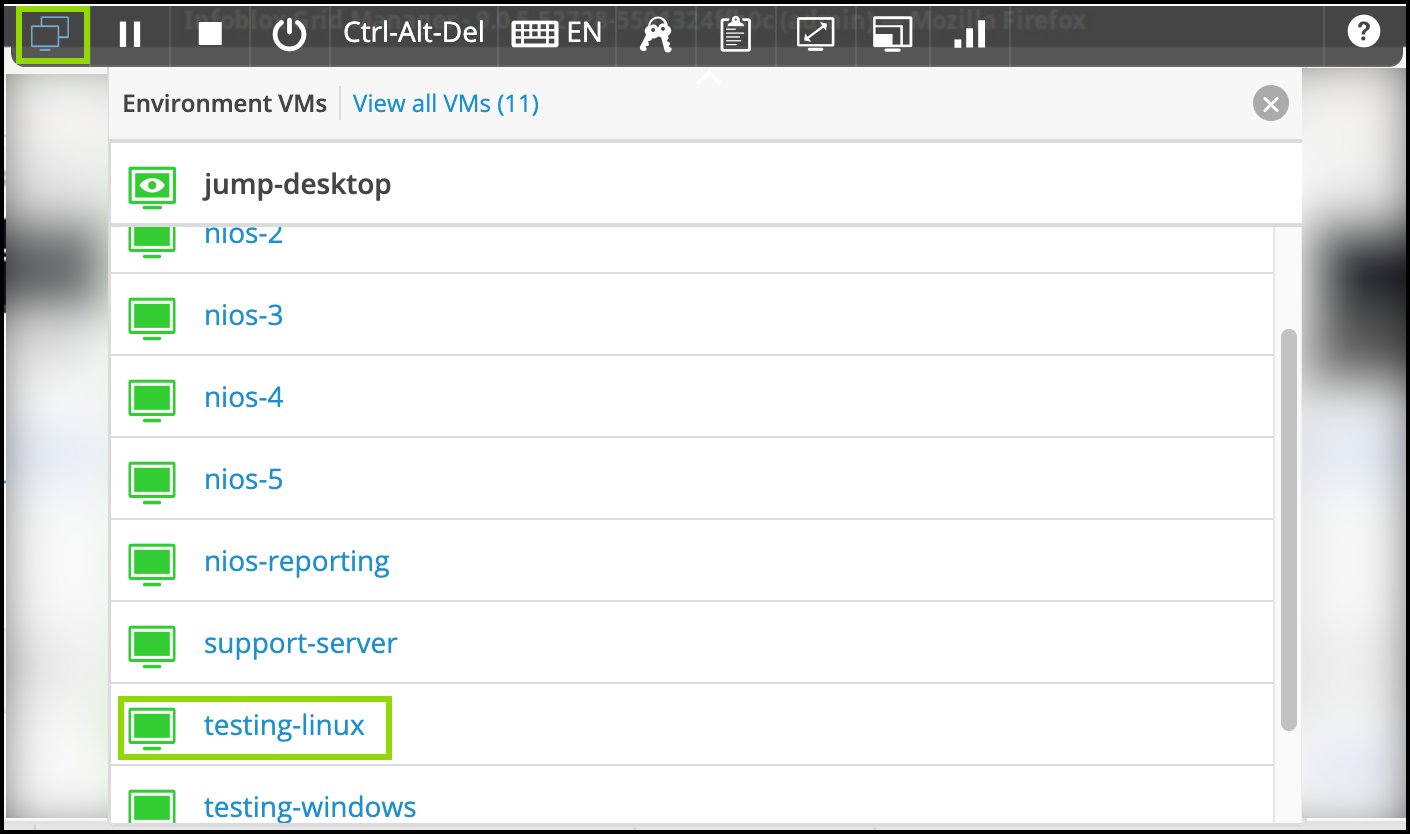
Switch over to the testing-linux machine with the credentials (training/infoblox) and set the machine up for testing.
-
open a terminal window and issue the command
sudo set-network-static-niosand verify that the machine now has the IP address 172.31.101.250 using the commandifconfig.
-
-
Use dig and syslog entries to validate the local RPZ configurations.
Solutions
Task 1 Solution: Create local RPZ - allowlist.rpz
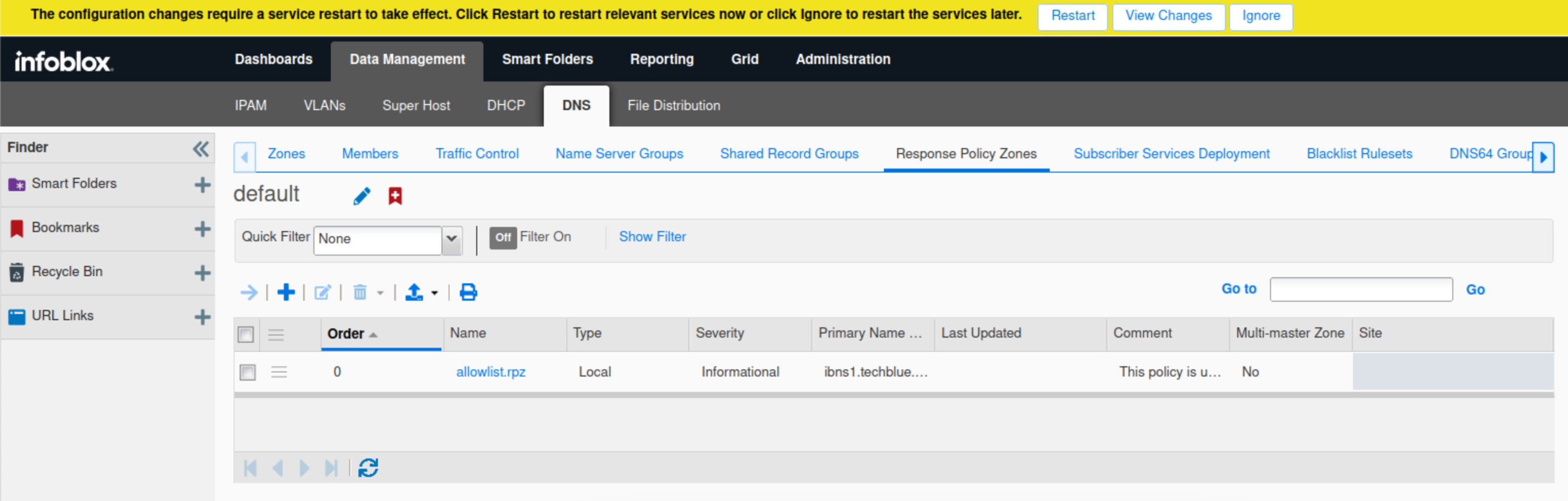
In this task, you create a local RPZ called allowlist.rpz. This will be used to ensure DNS traffic from the techblue.net domain is allowed to pass through.
-
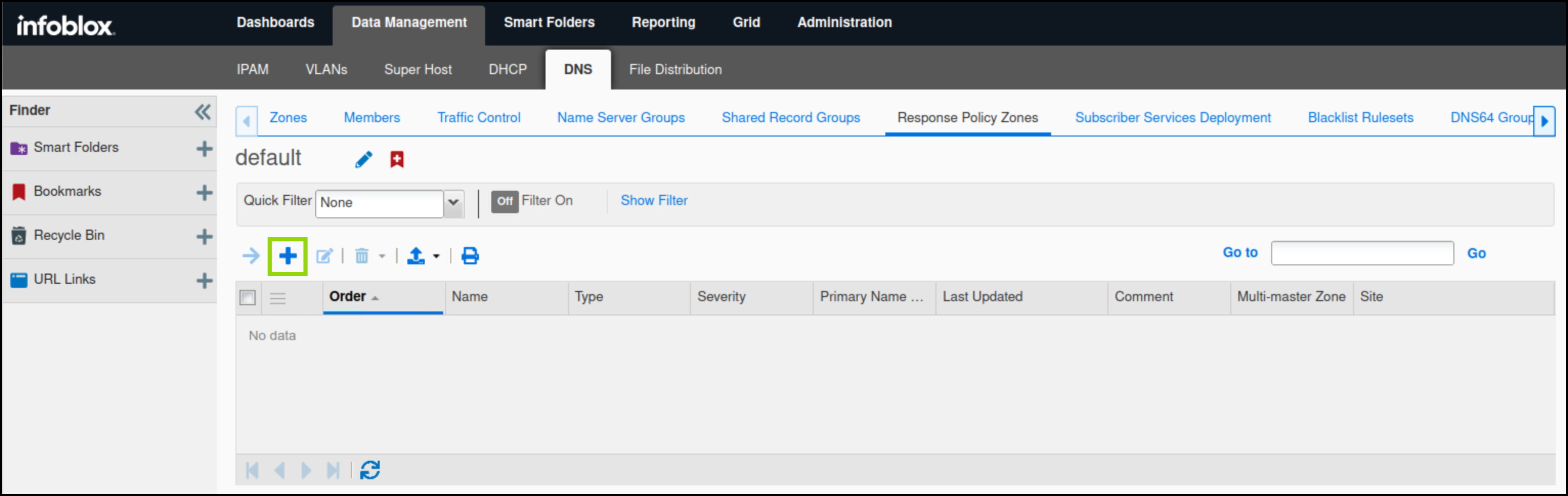
On the jump-desktop machine, open a browser window and access https://10.100.0.100.
-
Navigate to Data Management → DNS → Response Policy Zones.
-
Click the plus (+) symbol to add a new RPZ.
-
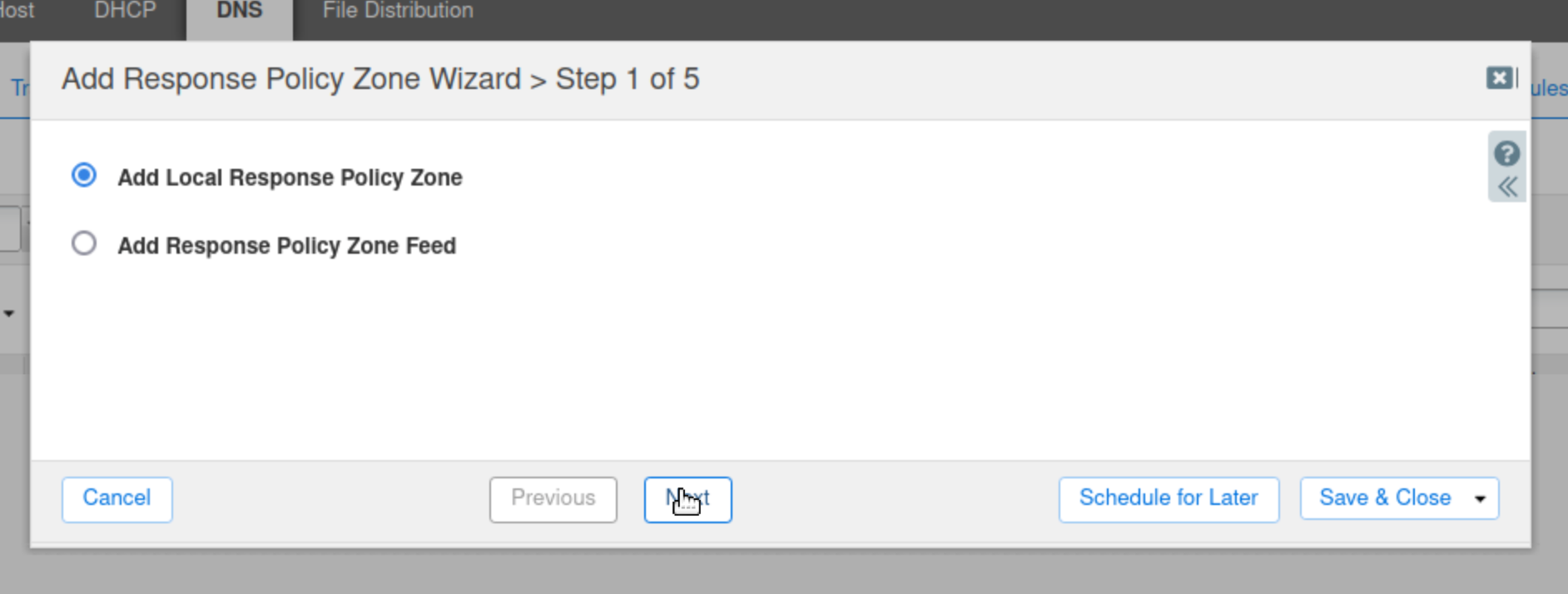
Select Add Local Response Policy Zone and click Next.
-
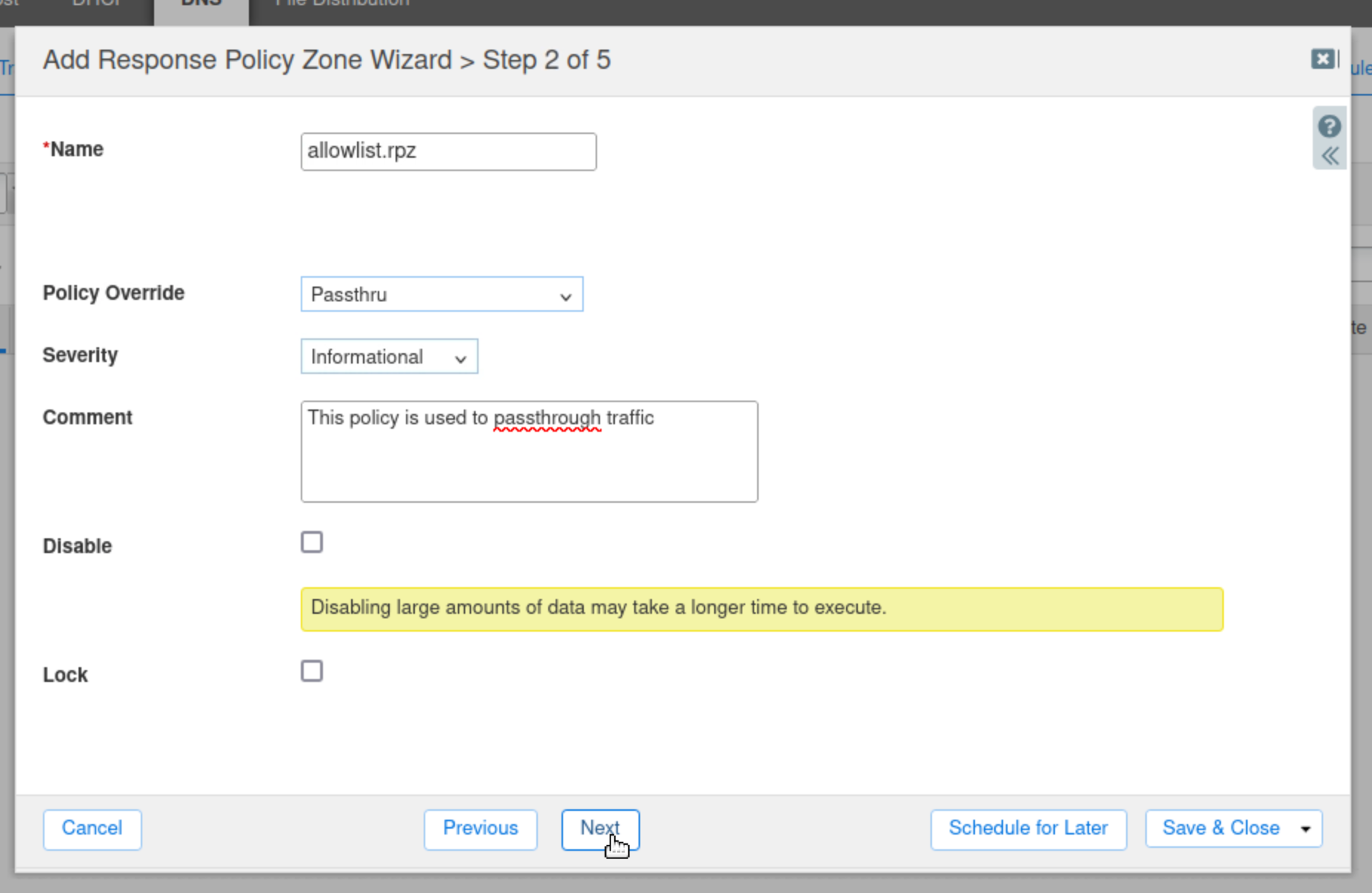
Enter allowlist.rpz for the name of the zone.
-
Set the Policy Override value to Passthru.
-
Change the Severity to Informational.
-
Type in a comment to describe the purpose of the RPZ.
-
Click Next to continue.
-
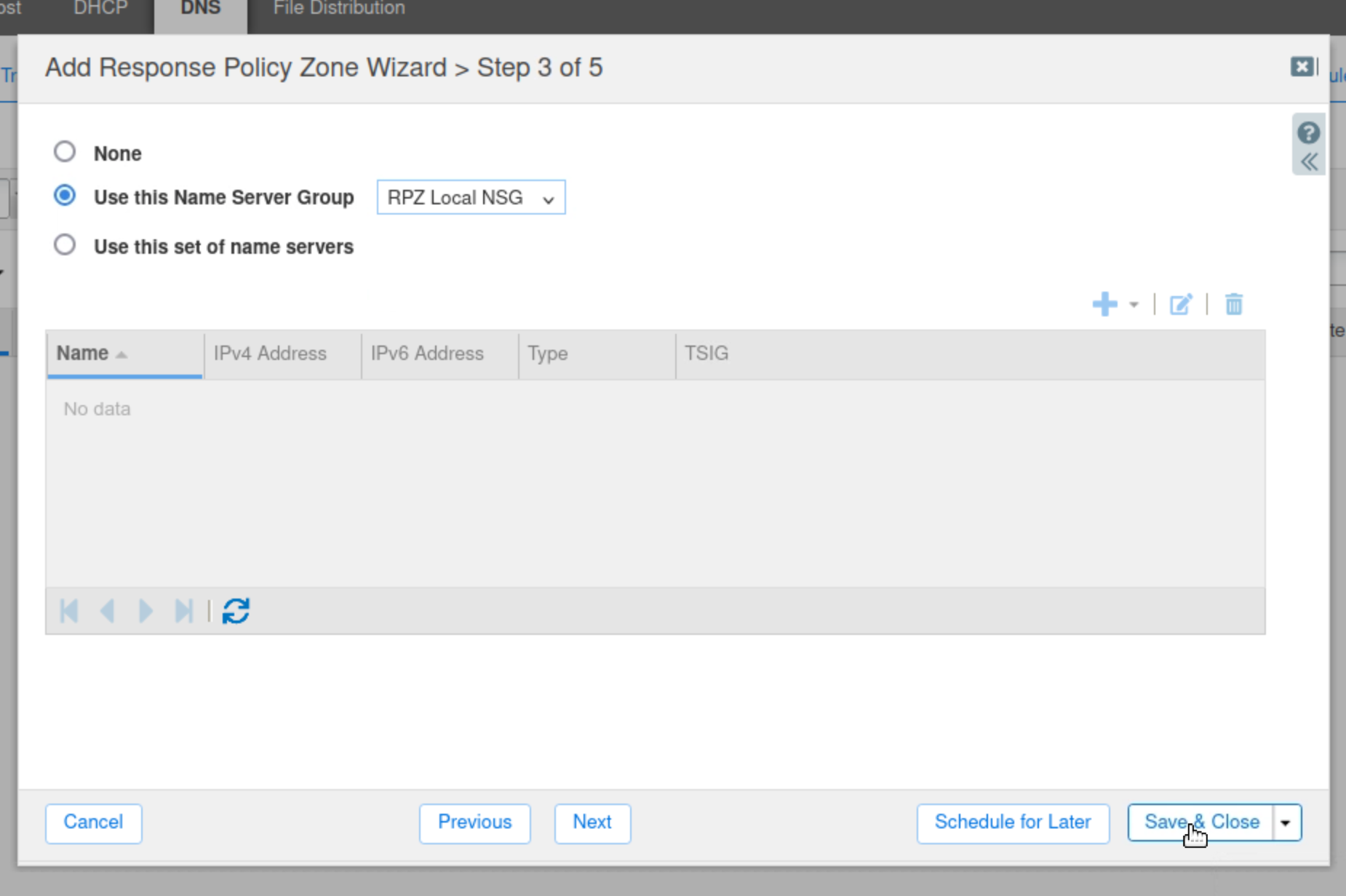
Select the Use this Name Server Group button.
-
Choose RPZ Local NSG from the drop-down list.
-
Click Save & Close.
-
Restart Services when prompted.
Task 2 Solution: Add Passthru Domain Policy Rules to allowlist.rpz
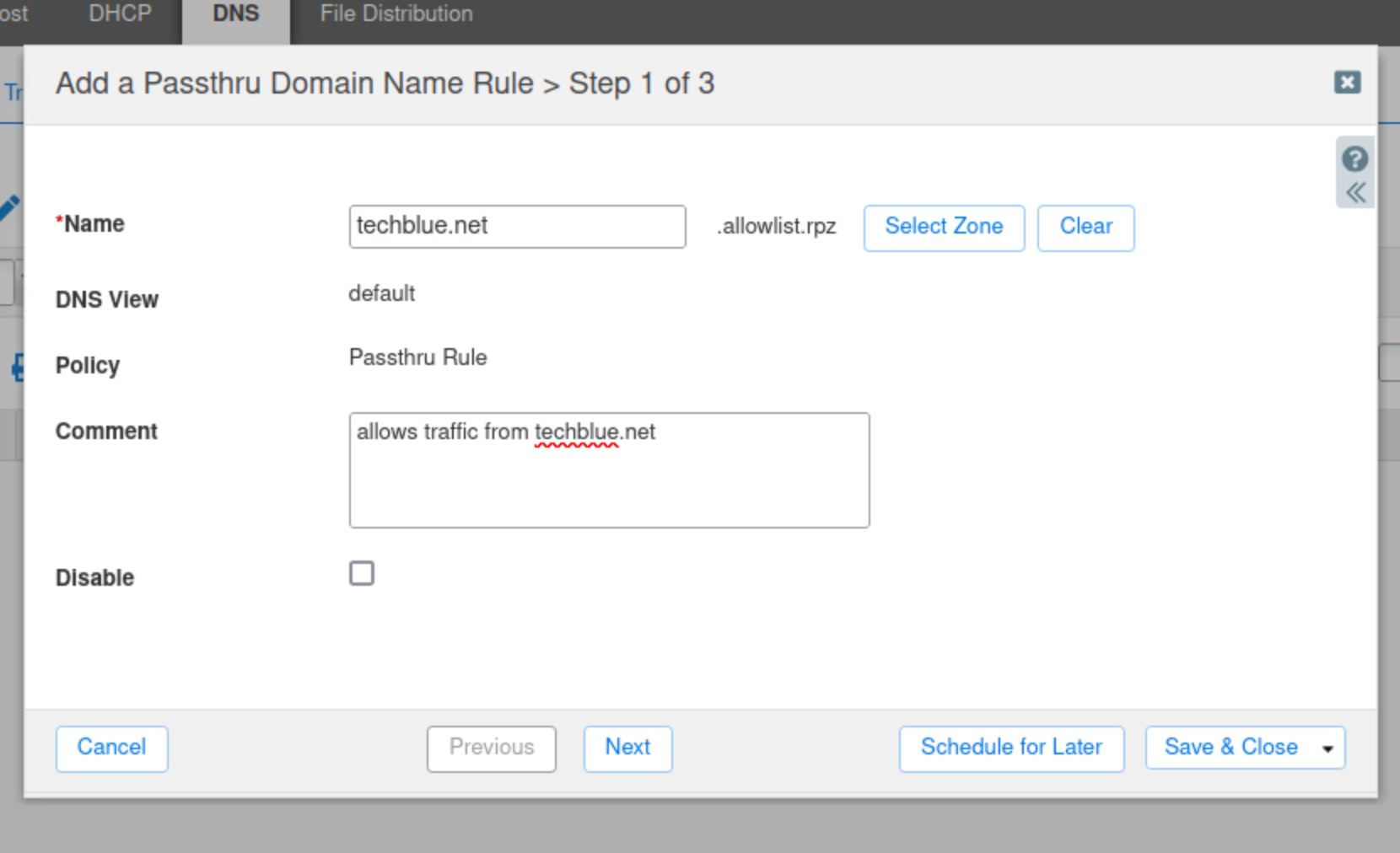
In this task, we create a rule in the allowlist.rpz policy to ensure that DNS requests for the techblue.net domain and all of its subdomains pass through unmodified. We will achieve that through two rules: the first will allow techblue.net, and the second will use the wildcard (*.techblue.net) to allow all subdomains.
-
Navigate to Data Management → DNS → Response Policy Zones.
-
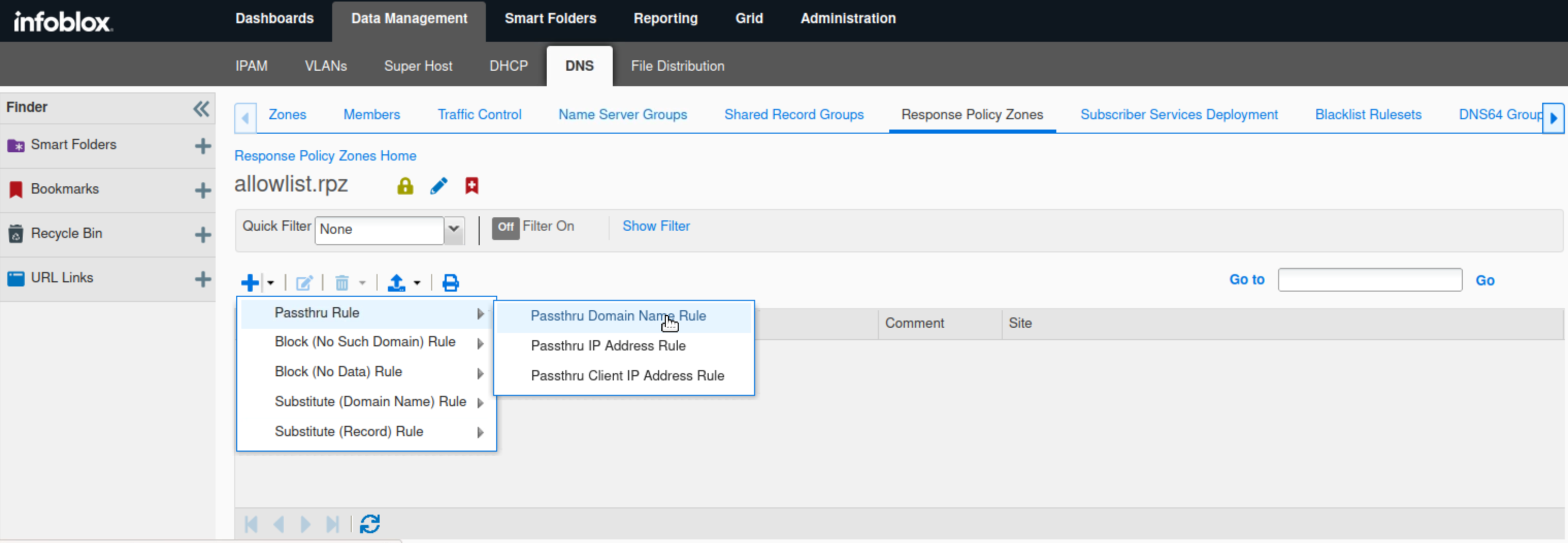
Click the link to allowlist.rpz.
-
Click the arrow next to the plus (+) symbol and select Passthru Rule from the drop-down list.
-
Select Passthru Domain Name Rule.
-
Enter techblue.net in the Name field.
-
Type a Comment to describe the purpose of the rule.
-
Click Save & Close.
-
Click the arrow next to the plus (+) symbol and select Passthru Rule from the drop-down list.
-
Select Passthru Domain Name Rule.
-
Enter *.techblue.net in the Name field.
-
Type a Comment to describe the purpose of the rule.
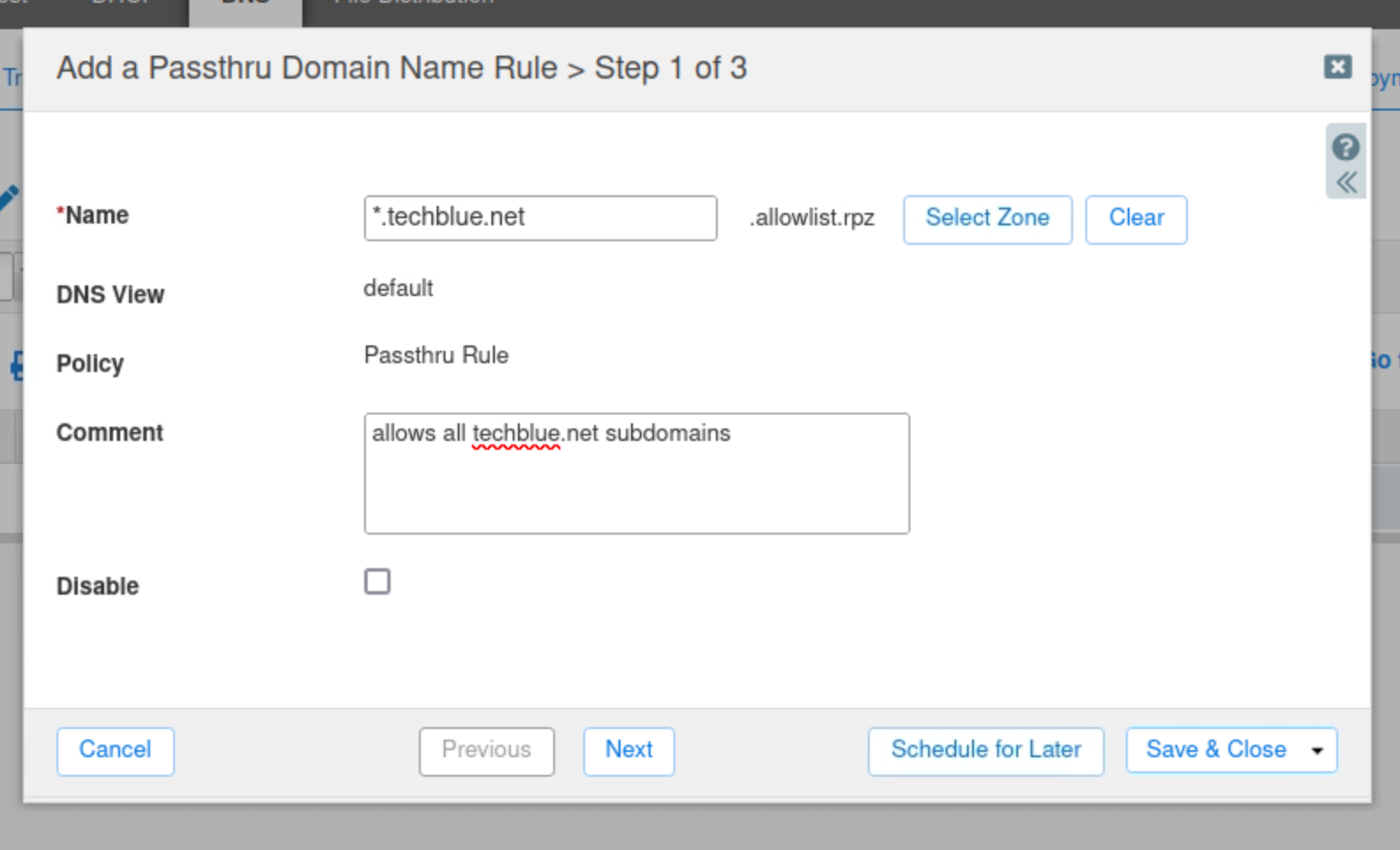
-
Click Save & Close.
Task 3 Solution: Test Pass-thru Local RPZ Rules
The newly created RPZ must be tested. In this task, we will use dig and syslog entries to validate the local RPZ configurations.
-
Switch over to the testing-linux machine with the credentials (training/infoblox) and set the machine up for testing.
-
open a terminal window and issue the command
sudo set-network-static-niosand verify that the machine now has the IP address 172.31.101.250 using the commandifconfig.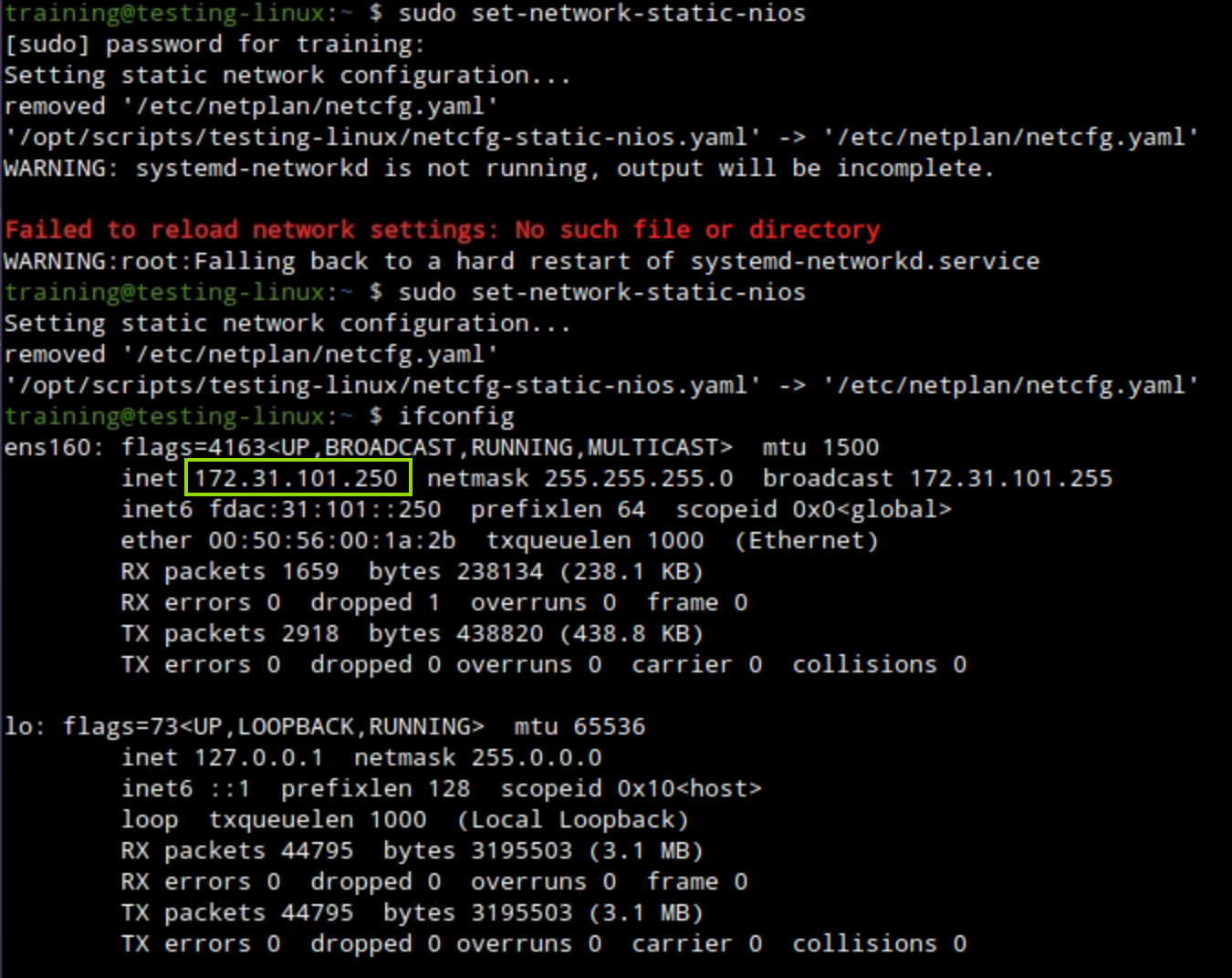
-
-
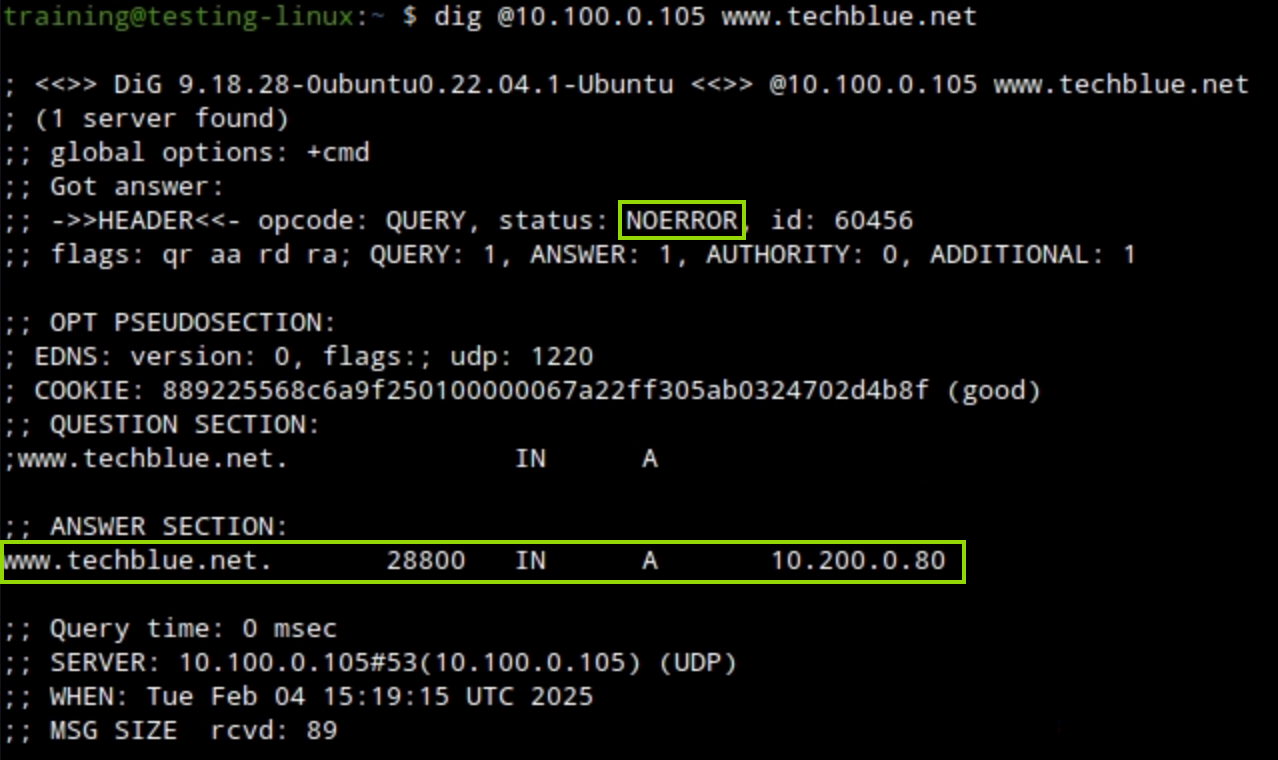
Open a terminal window on testing-linux. Use the dig command
dig @10.100.0.105 www.techblue.netto perform a DNS query for www.techblue.net.-
10.100.0.105 is the IP address of ibns1.techblue.net an HA pair grid member.
-
The results show that the query has been answered. The IP Address of www.techblue.net is 10.200.0.80.
-
-
Switch back the the jump-desktop machine.
-
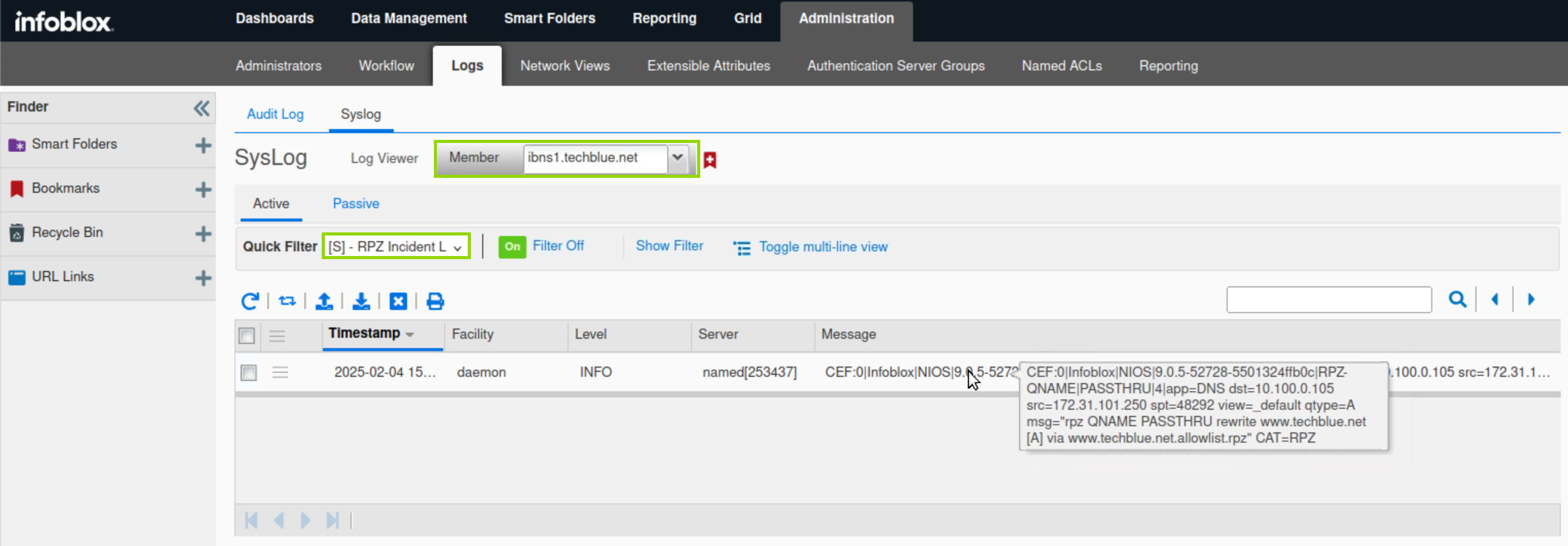
Navigate to Administration → Logs → Syslog.
-
Select the Member ibns1.techblue.net from the drop-down list.
-
Choose RPZ Incidents from the Quick Filter drop-down list.
-
The DNS Query for www.techblue.net is listed in the messages section, in CEF format.
-
The query has matched a PASSTHRU rule in allowlist.rpz.
-