Scenario
Your network team informs you that a new zone has been configured on the load balancer, the load balancer is polaris.techblue.io. The name of the new zone is gslb.cdat.training.infoblox.com. You are tasked with configuring both ibns1 and ibns2 to hold a read-only copy of this zone.
Configure both Grid members (ibns1) and (ibns2) to be secondary name servers for this zone.
Estimate Completion Time
-
30 to 40 minutes
Credentials
|
Description |
Username |
Password |
URL or IP |
|---|---|---|---|
|
Grid Manager UI |
admin |
infoblox |
Requirements
-
Administrative access to the Grid
Learning Content
Lab Initiation
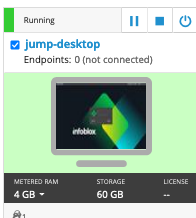
Access jump-desktop
Once the lab is deployed, you can access the virtual machines required to complete this lab activity. To initiate the lab, click on the jump-desktop tile and login to the Linux UI:
Username: training
Password: infoblox
Initiate lab
To initiate the lab, double-click the Launch Lab icon on the Desktop.
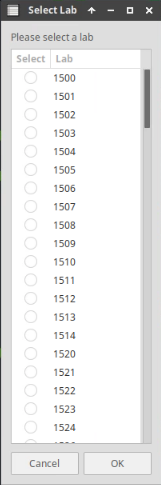
Choose the lab number from the list and click OK.
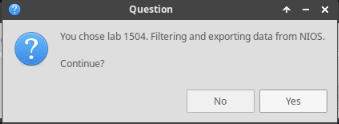
After clicking OK, you will see a pop-up message with a brief description of the lab task. If the description looks correct, click Yes to continue lab initiation.
Lab initiation will take a couple of minutes to finish.
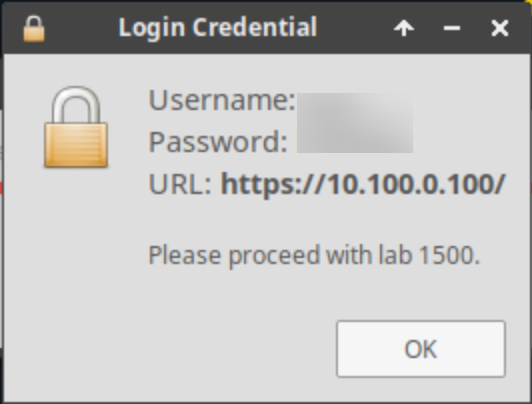
Once complete, you will see another pop-up message with the login credentials and the URL for the Grid Manager’s User Interface. Note that the credentials may differ from those from prior labs.
Tasks
To complete this lab, you need to perform the following tasks.
-
Add secondary authoritative zone
-
Troubleshoot name resolution issue
Task 1: Configure your Grid Members as Secondaries
Configure both Grid members (ibns1) and (ibns2) to be secondary name servers for gslb.cdat.training.infoblox.com. Use the dig command on the jump-desktop VM to identify the current IP address of polaris.techblue.io.
Task 2: Troubleshoot Name Resolution
After you have setup the secondary zone on both members (ibns1) and (ibns2), users report when they query (ibns1), the name www.gslb.cdat.training.infoblox.com resolves, but not when queried against (ibns2). Please troubleshoot and find the root cause.
Hint: Use the following commands for lookup:
Lookup using member ibns1: dig @10.100.0.105 www.gslb.cdat.training.infoblox.com.
Lookup using member ibns2: dig @10.200.0.105 www.gslb.cdat.training.infoblox.com.
Solutions
Task 1 Solution: Configure your Grid Members as Secondaries
-
First, verify the primary master name server by retrieving the SOA record
-
This will identify the primary as polaris.techblue.io.
-
-
Run the following command from the terminal on the jump-desktop VM to identify the current IP address of polaris.techblue.io:
dig +short polaris.techblue.io. -
Create an Authoritative Forward-Mapping zone for
gslb.cdat.training.infoblox.com.-
Specify polaris.techblue.io as the External Primary.
-
Specify ibns1 and ibns2 as Grid Secondaries.
-
-
Verify in Grid Manager UI by navigating to Data Management → DNS → Zones → gslb.cdat.training.infoblox.com. The zone data should load, and you can see the records configured in the zone.
-
You should also verify by performing a lookup against ibns1 to verify the AA flag is present (indicating an authoritative answer)
$ dig @10.100.0.105 gslb.cdat.training.infoblox.com. ; <<>> DiG 9.18.24-0ubuntu0.22.04.1-Ubuntu <<>> @10.100.0.105 gslb.cdat.training.infoblox.com. ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 10496 ;; flags: qr aa rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 1220 ; COOKIE: 68f1ea1cb9b7f91a0100000066d82f8ecb3e5f5ee57de161 (good) ;; QUESTION SECTION: ;gslb.cdat.training.infoblox.com. IN A ;; AUTHORITY SECTION: gslb.cdat.training.infoblox.com. 900 IN SOA polaris.techblue.io. training-tech.infoblox.com. 3 10800 3600 2419200 900 ;; Query time: 0 msec ;; SERVER: 10.100.0.105#53(10.100.0.105) (UDP) ;; WHEN: Wed Sep 04 09:59:42 UTC 2024 ;; MSG SIZE rcvd: 169
Task 2 Solution: Troubleshoot Name Resolution
-
Resolution of gslb.cdat.training.infoblox.com against ibns1 should be successful.
-
AAflag will be set in dig as ibns1 is authoritative for the zone.
-
-
Resolution of gslb.cdat.training.infoblox.com against ibns2 will fail with SERVFAIL error message.
-
Member (nios-4) is unable to transfer zone cdat.training.infoblox.com
-
Performing standard dig queries against gslb.cdat.training.infoblox.com from ibns2 will work such as
dig @polaris.techblue.io. www.gslb.cdat.training.infoblox.com. -
Using dig on ibns2 with +tcp or +vc option set will cause the query to fail/timeout.
-
Using dig on ibns2 to request a manual zone transfer (AXFR) will fail/timeout (
dig @polaris.techblue.io. gslb.cdat.training.infoblox.com. AXFR)
-
This is proof that TCP/53 is blocked, preventing zone transfer from Polaris to ibns2.