Installing and Managing Infoblox Endpoints (2804)
New Infoblox Portal Navigation - Read First
The Infoblox Portal UI has changed. Lab steps and screenshots may not match what you see. You MUST review the navigation mapping table before starting to successfully complete this content.
Scenario
To extend Threat Defense coverage to roaming users, your organization enables Infoblox Endpoint protection on user devices, including laptops, company-managed smartphones, and handheld devices. This ensures DNS traffic from mobile and remote endpoints is secured, even outside the corporate network.
You are tasked with the following:
Deploy the Infoblox Endpoint agent on a Windows machine.
Create a new Endpoint Group in the Infoblox Portal.
Add the deployed endpoint to an Endpoint group.
The Endpoint Group will later be added to a security policy for testing and validation.
Estimated Completion Time
20 to 30 mins
Prerequisites
Administrative access to the Infoblox Portal
Tasks
Install the Infoblox Endpoint agent on a Windows VM.
Create an Endpoint Group in Infoblox Portal.
Add the Windows Endpoint to the Endpoint Group.
Task 1: Installing Infoblox Endpoint
In testing-windows, open the Tools folder on the Desktop and run the interface-static-internet.bat file as an administrator. This sets a static IP address for the VM. Please re-enter the command if the VM does not get an IP address the first time.
Log in to your lab’s testing-windows VM. Then, launch a web browser and use your Education Infoblox Portal Credentials to log into the Infoblox Portal. Download the correct Endpoint version for your Windows machine, extract and install the Infoblox Endpoint agent in testing-windows, and verify that the Endpoint was added.
Task 2: Creating an Endpoint Group
In the Infoblox Portal, create an endpoint group named Techblue Endpoints.
Task 3: Adding the Windows endpoint to Techblue-Endpoints
In the Infoblox Portal, add the testing-windows Endpoint into the Techblue Endpoints Endpoint Group.
Solutions
Task 1 Solution: Installing Infoblox Endpoint
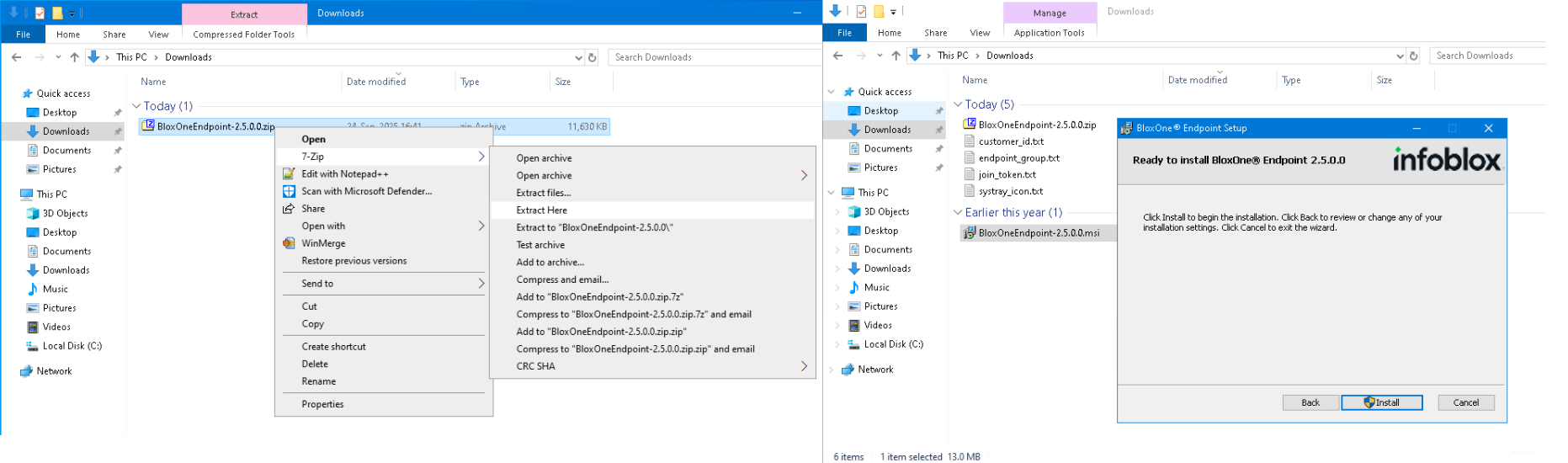
Extract all files in the same folder, or the installation process will fail. The included files contain the information required to connect the endpoint agent to your Infoblox Threat Defense tenant, such as the Join Token; without them, the installation cannot succeed.
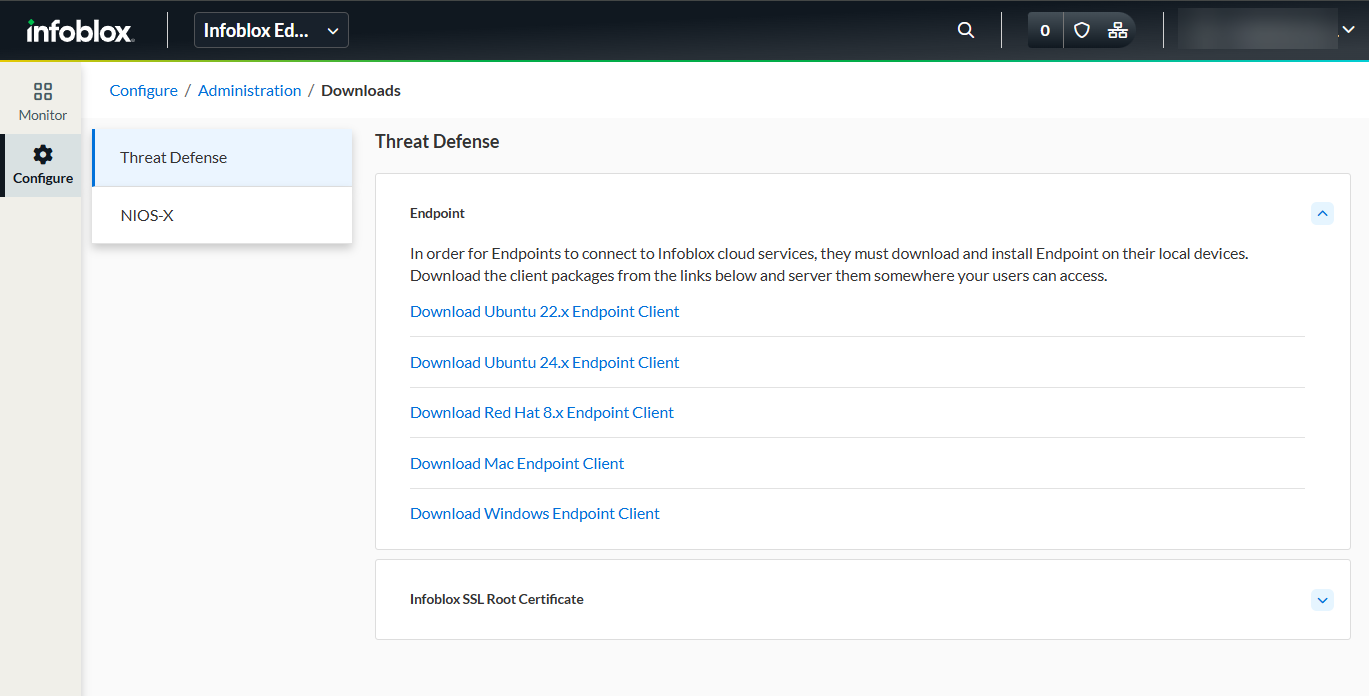
In this task, we will download the Windows installation package for the Infoblox Endpoint client from the Infoblox Portal, extract it, and install it on one of our lab’s virtual machines, testing-windows.
Log into your lab’s testing-windows, with the credentials
training / infoblox.Open the Tools folder on the Desktop and run the
interface-static-internet.batas an administrator.NOTE: This file is used to set an IP address for the VM in a subnet simulating a direct internet connection.
In testing-windows, open a browser and use your Education Infoblox Portal Credentials to log into the Infoblox Portal.
Navigate to Configure → Administration → Downloads → Threat Defense → Endpoint.
Download the correct Endpoint version for your Windows machine.
Extract the zip components into one folder using 7-Zip.
Right-click the zip file and choose 7-Zip → Extract Here.
Install Infoblox Endpoint Agent using the .msi executable.
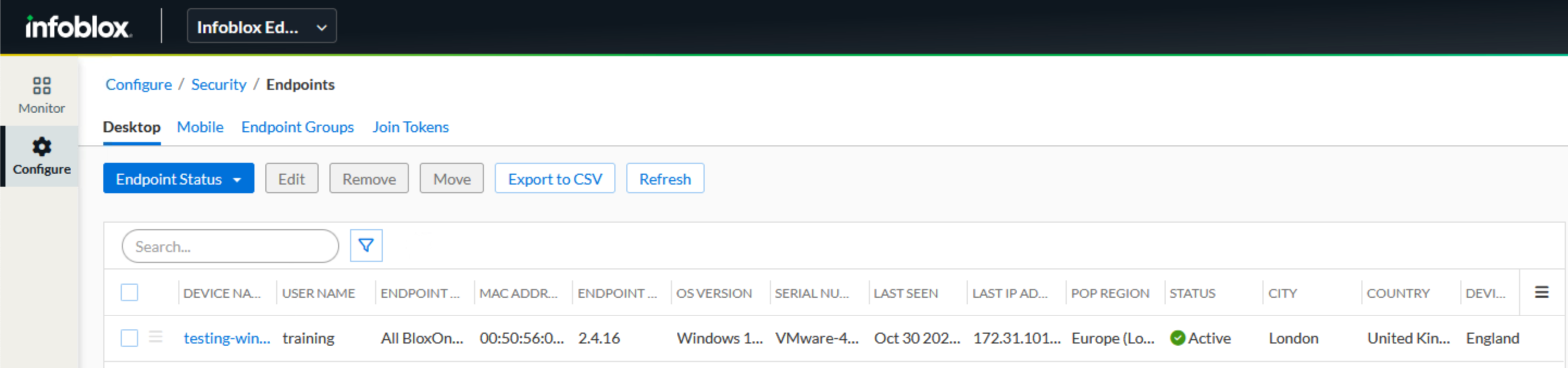
In the Infoblox Portal, navigate to Configure → Security → Endpoints → Desktop and verify that the Endpoint was added.
Task 2 Solution: Creating an Endpoint Group
In this task, we will create a new Endpoint Group named Techblue Endpoints, which will be added in later labs as a Security Policy Network Scope.
In the Infoblox Portal, navigate to Configure → Security → Endpoints → Endpoint Groups.
Click Create Endpoint Group, give the name
Techblue Endpoints, then click Save & Close.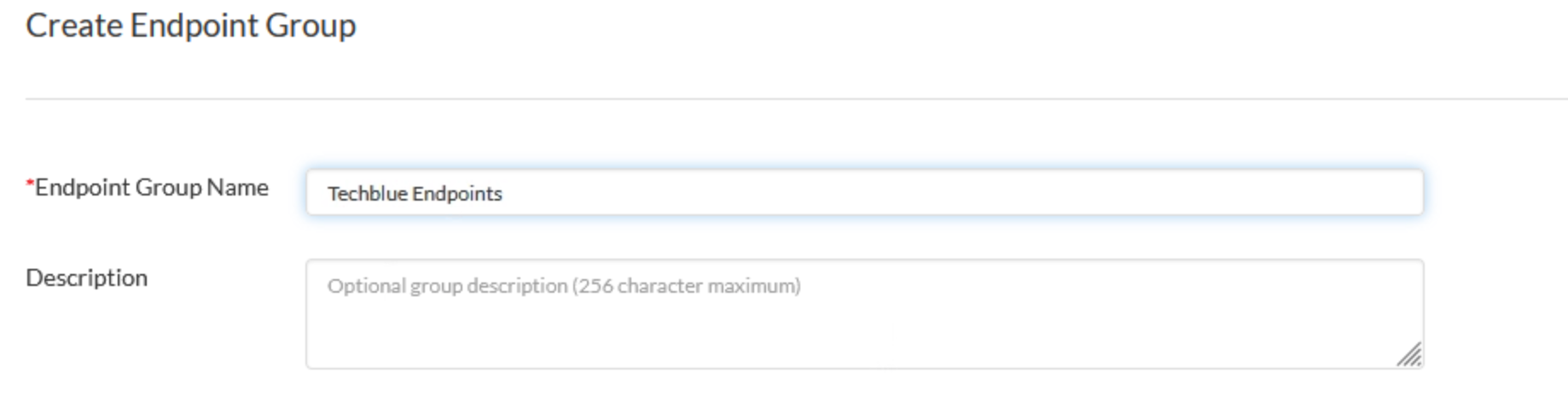
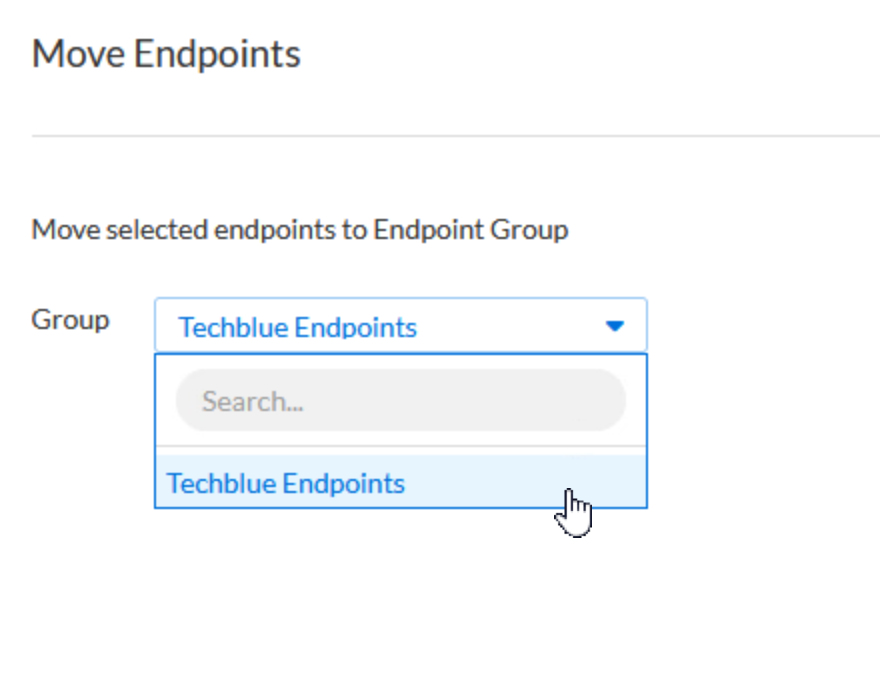
Task 3 Solution: Adding the Windows endpoint to Techblue-Endpoints
In this task, we will move our endpoint, which we installed earlier on testing-windows, from the default endpoint group to Techblue Endpoints.
In the Infoblox Portal, navigate to Configure → Security → Endpoints →Desktop page, select the endpoint, and click Move.
Select Techblue Endpoint Group and click Move.