Using Application Discovery Reports (2809)
New Infoblox Portal Navigation - Read First
The Infoblox Portal UI has changed. Lab steps and screenshots may not match what you see. You MUST review the navigation mapping table before starting to successfully complete this content.
Scenario
You are a security analyst responsible for monitoring application activity across your organization’s network. Your SOC relies on Infoblox Threat Defense to identify unusual or unauthorized application usage.
Your environment is configured with DNS Forwarding Proxy, and all traffic from internal devices flows through Threat Defense for inspection.
To support ongoing threat‑hunting and organizational compliance efforts, you will classify business‑relevant applications as Approved, mark all other discovered applications as Unapproved, and then use Application Discovery Reports to identify usage trends, potential shadow IT applications, and devices generating high‑volume requests.
Estimate Completion Time
20-30 Minutes
Learning Content
Before starting, review the following learning materials to reinforce the core concepts used in this lab:
Prerequisites
Administrative access to the Infoblox Portal
Enabling the DNS Forwarding Proxy Service (DFP) on a NIOS-X Server (2802)
Tasks
Task 1: Classify applications as Approved or Unapproved
You will classify detected applications into two groups:
Applications required for day‑to‑day business operations will be marked Approved, while all other applications will be marked Unapproved.
This ensures your SOC can quickly identify potential high‑risk or unwanted applications.
Set Applications categories as Approved when found:
Google Search
Communication Applications: Slack and Teams.
Microsoft OneDrive
Grammarly
Security Applications: Duo, Microsoft Certificates, and Windows Defender
Windows Update
Set the rest of the Applications as Unapproved
Task 2: Monitor Applications using Application Discovery Reports
You will use the Application Discovery Summary, Categories, Applications, and Devices views to identify: The most frequently used applications, The most common application categories, Unapproved applications in use, Devices responsible for the most application traffic. This provides SOC‑aligned visibility into usage patterns and potential risks.
Solutions
Task 1 Solution: Mark applications as Approved or Unapproved
In this task, we will mark detected applications in our environment as either approved or unapproved. This is to allow us to easily identify any unwarranted or potentially malicious applications being used in our organization. We will add business-relevant applications to the approved group, and any other application will be marked as Unapproved.
Log in to your lab’s jump-desktop.
Use your Education Infoblox Portal Credentials to log into the Infoblox Portal.
Navigate to Monitor → Reports → Security → Application Discovery
Note that all applications are currently listed under the Needs Review category.
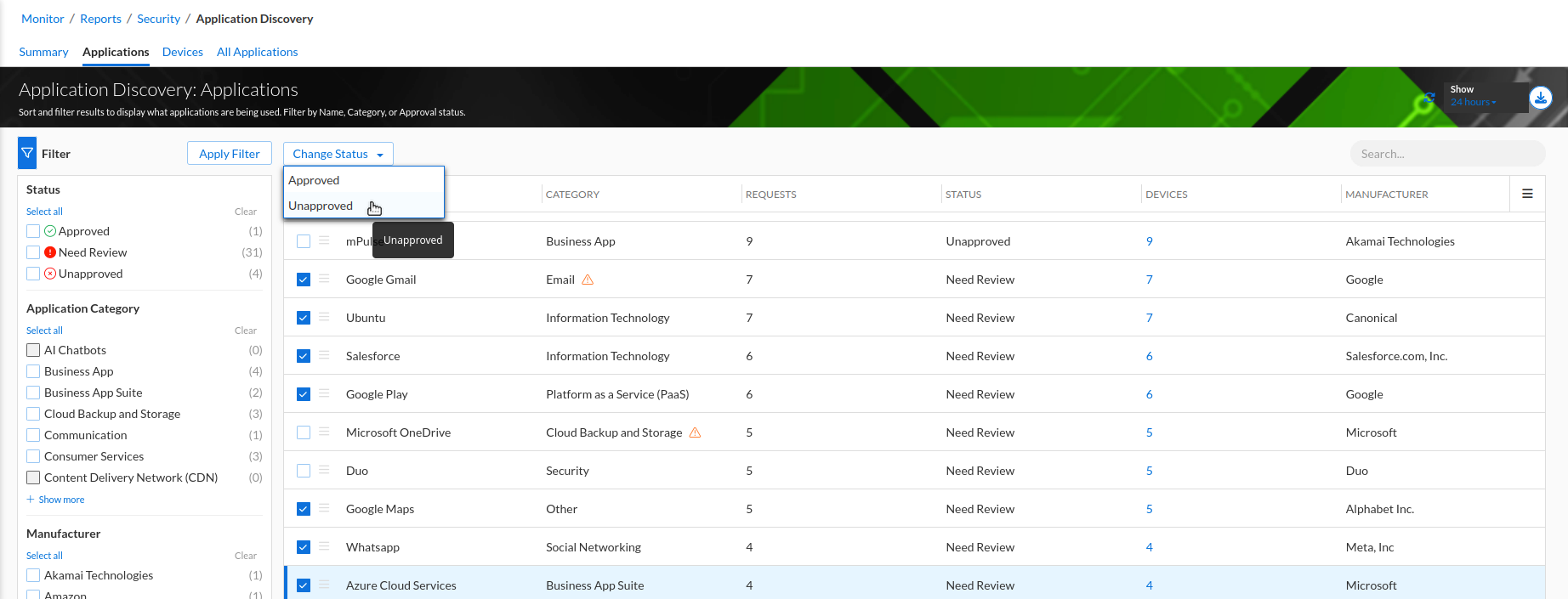
Select the Applications tab (or click View all Detected Applications).
Mark the following as Approved by selecting each entry and choosing Approved when found:
Google Search
Communication Applications: Slack and Teams.
Microsoft OneDrive
Grammarly
Security Applications: Duo, Microsoft Certificates, and Windows Defender
Windows Update
Mark all remaining discovered applications as Unapproved.
Task 2 Solution: Monitor Applications using Application Discovery Reports
Please note that your report data might not exactly match the screenshots and answers provided
Now that applications are classified, you will use Application Discovery Reports to evaluate usage trends, identify shadow IT, and detect devices associated with suspicious traffic patterns
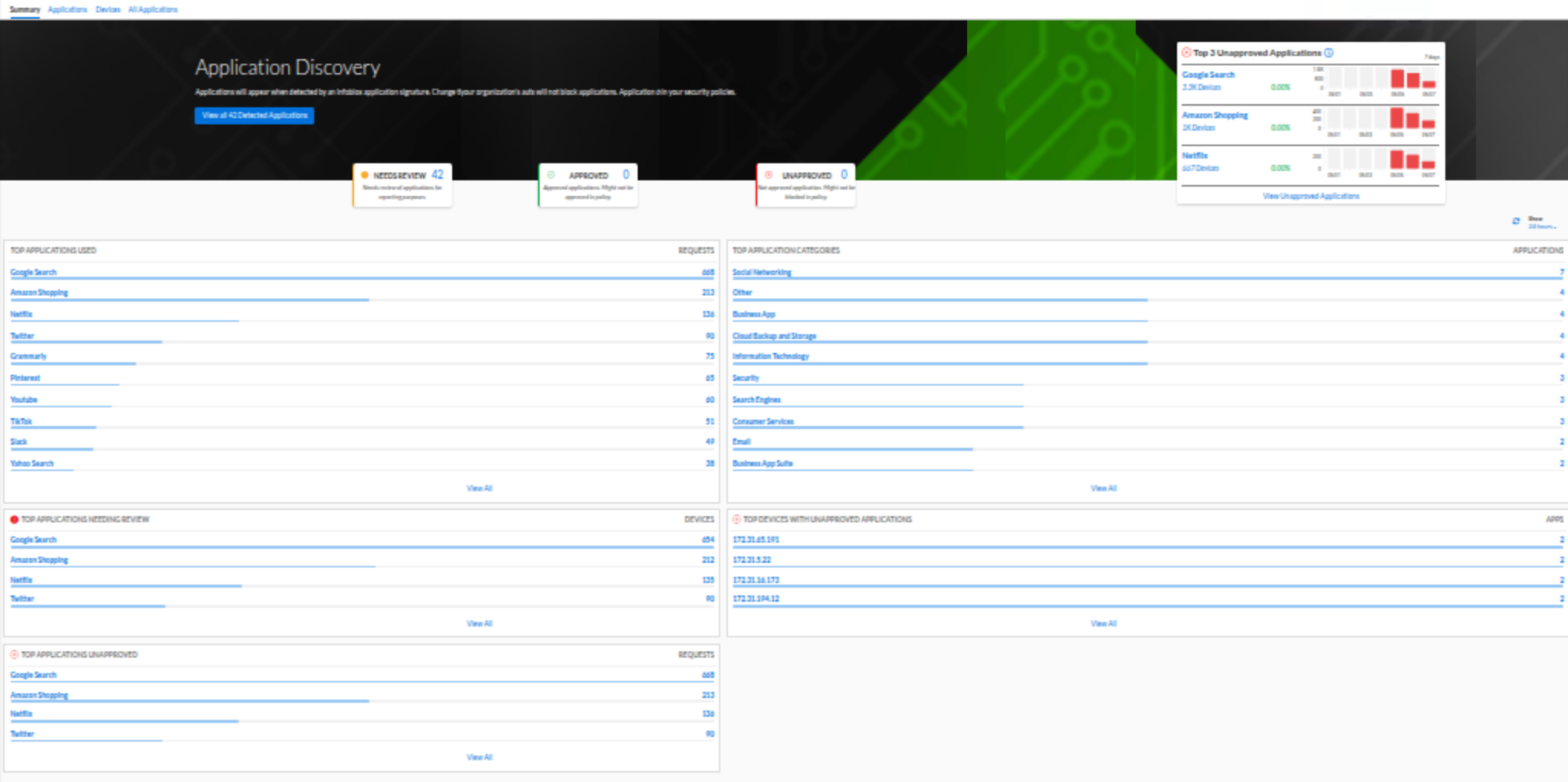
Navigate to the Summary tab
Under the TOP APPLICATIONS USED widget, identify the three applications with the highest request volume.
In our example report, the results include:
Google Search at 229 requests
Amazon Shopping at 64 requests
Netflix at 38 requests
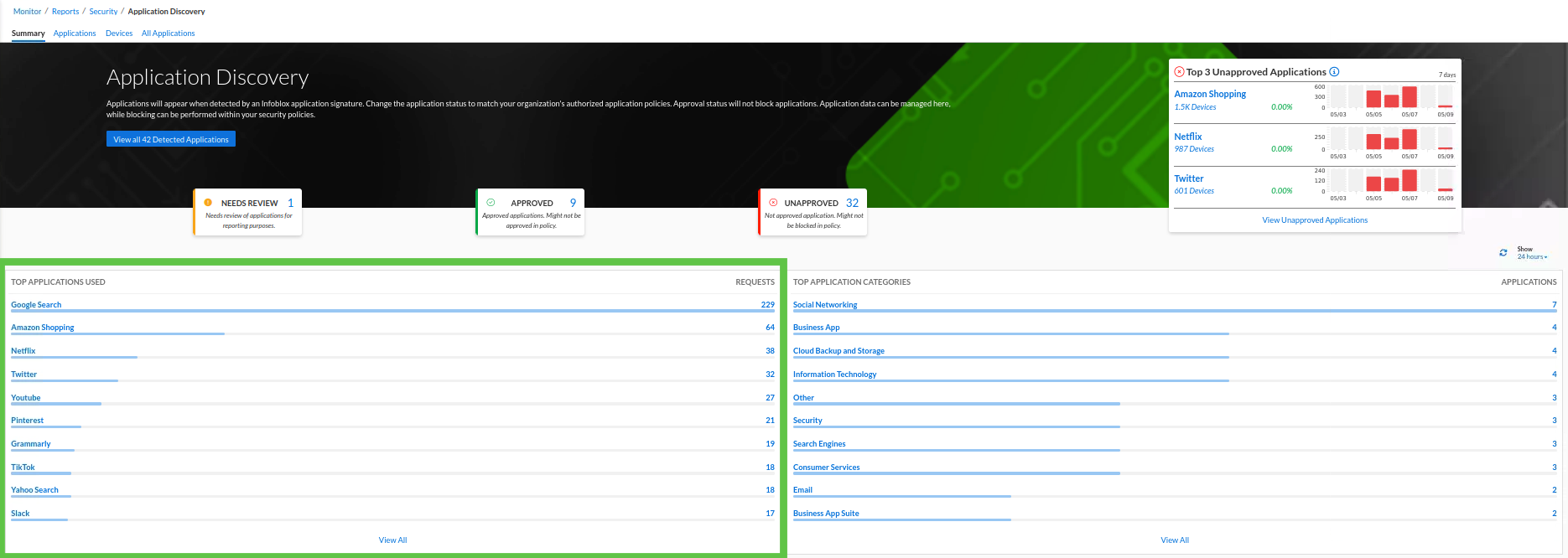
Under the TOP APPLICATIONS CATEGORIES widget, review the three most common categories.
In our example report, the results include:
Social Networking at 7 Applications
Business Apps at 4 Applications
Cloud Backup and Storage at 3 Applications
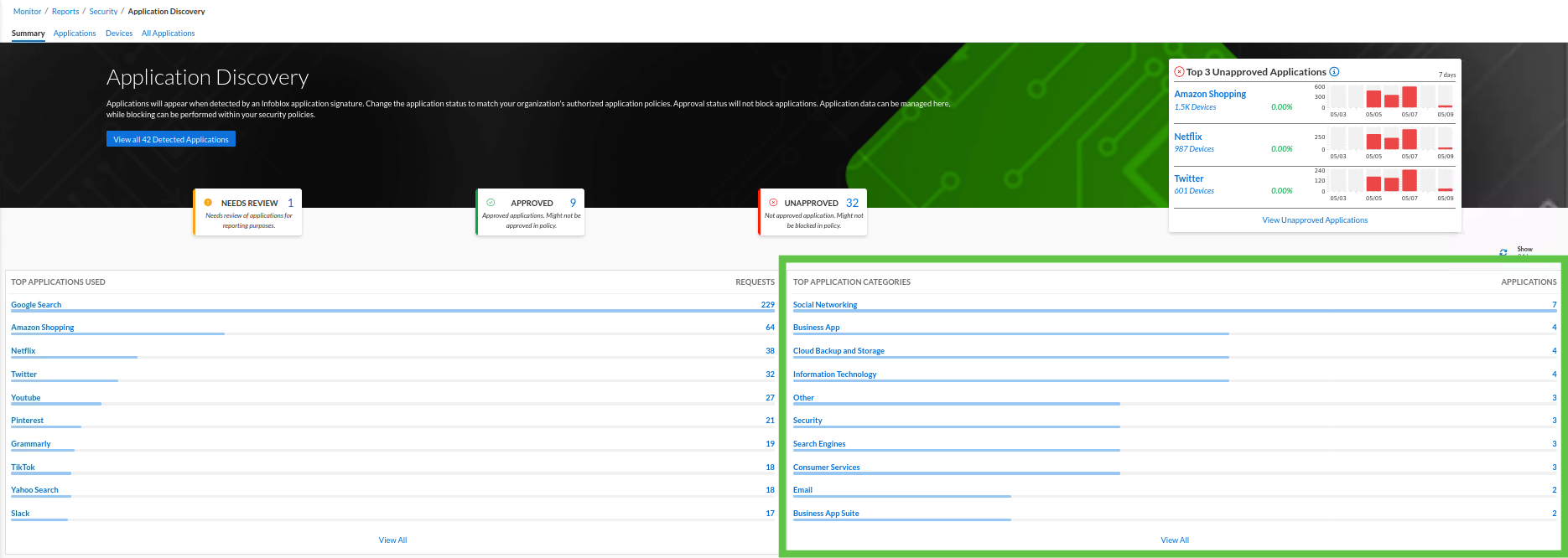
Under the Top 3 Unapproved Applications widget, identify the three most heavily used unapproved applications.
In our example report, the results include:
Amazon Shopping with 1.5k devices
Netflix with 987 Devices
Twitter with 601 Devices
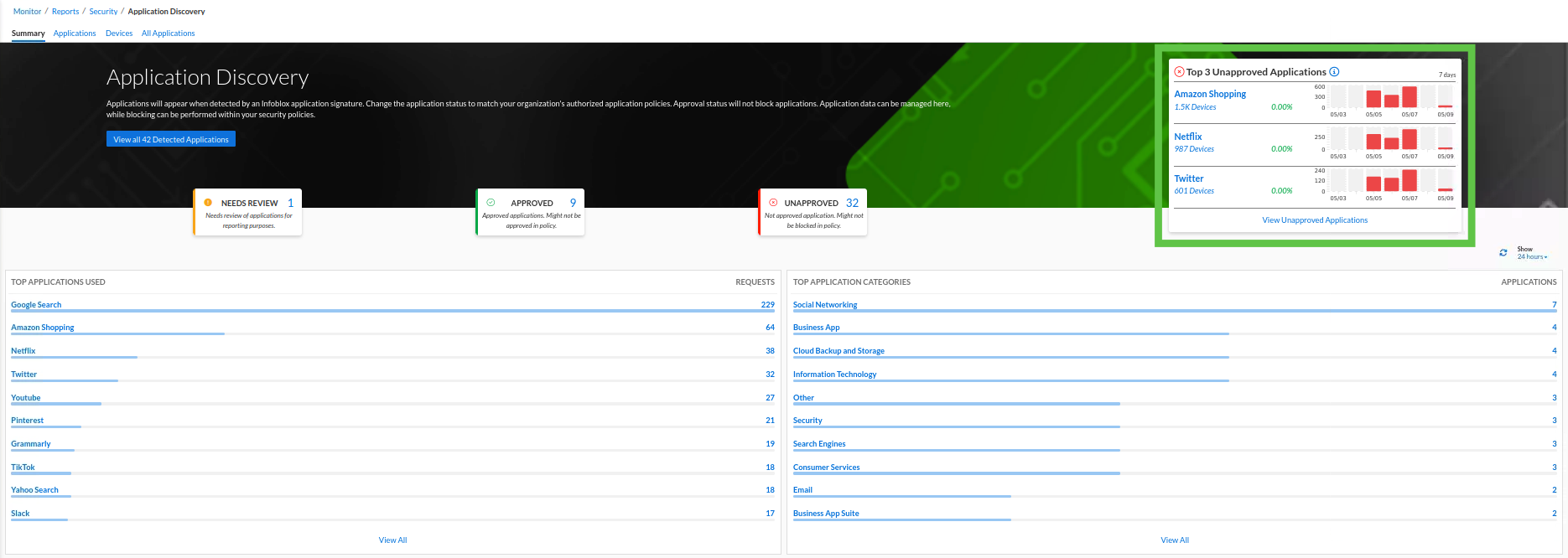
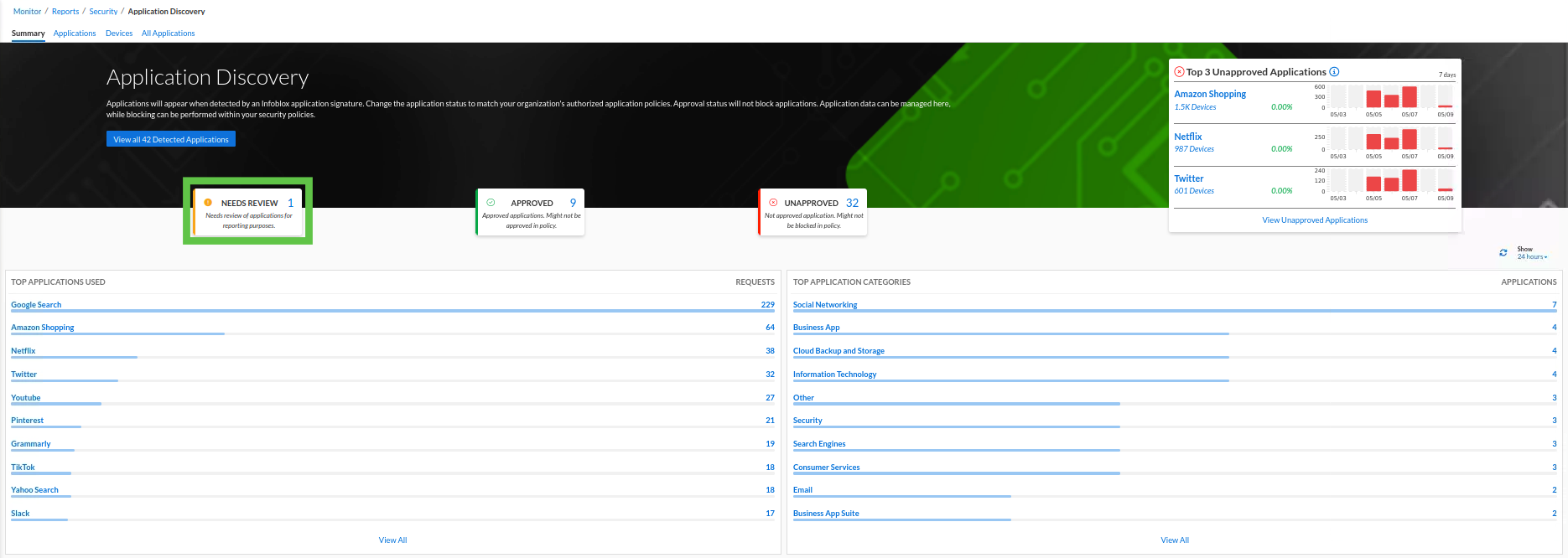
Under the NEEDS REVIEW card, verify whether any applications still require classification.
In our example report, yes, we have one application that still needs to be reviewed.
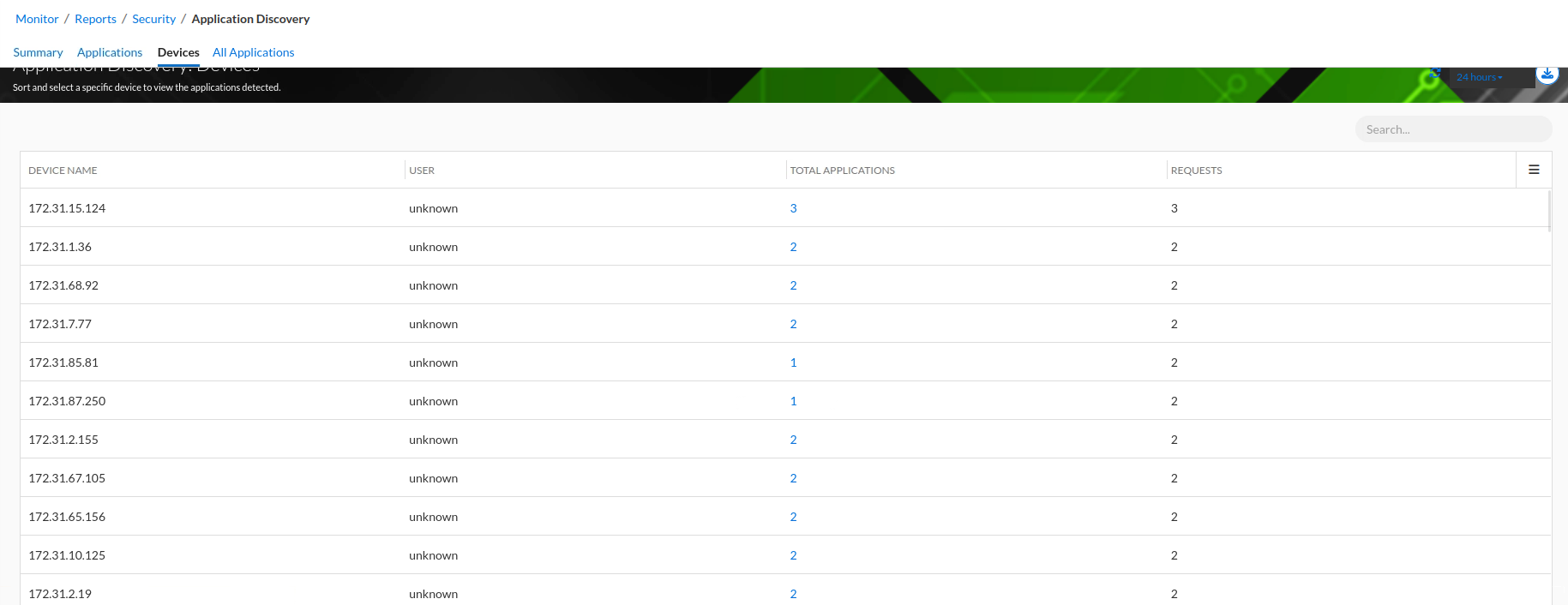
Navigate to the Devices tab
Identify the top three device IPs generating the highest application traffic. In our example, the IPs are:
172.31.15.124
172.31.1.36
172.31.7.77